How does Cisco Stealthwatch Cloud provide security for cloud environments?
Which API is used for Content Security?
An MDM provides which two advantages to an organization with regards to device management? (Choose two)
Which function is the primary function of Cisco AMP threat Grid?
An engineer is trying to securely connect to a router and wants to prevent insecure algorithms from being used.
However, the connection is failing. Which action should be taken to accomplish this goal?
Which feature requires a network discovery policy on the Cisco Firepower Next Generation Intrusion Prevention
System?
A company is experiencing exfiltration of credit card numbers that are not being stored on-premise. The
company needs to be able to protect sensitive data throughout the full environment. Which tool should be used
to accomplish this goal?
Which IPS engine detects ARP spoofing?
Which two risks is a company vulnerable to if it does not have a well-established patching solution for
endpoints? (Choose two)
The main function of northbound APIs in the SDN architecture is to enable communication between which two areas of a network?
Which telemetry data captures variations seen within the flow, such as the packets TTL, IP/TCP flags, and payload length?
In a PaaS model, which layer is the tenant responsible for maintaining and patching?
Which capability is exclusive to a Cisco AMP public cloud instance as compared to a private cloud instance?
What are two rootkit types? (Choose two)
Which algorithm provides encryption and authentication for data plane communication?
What is a characteristic of Firepower NGIPS inline deployment mode?
Which two characteristics of messenger protocols make data exfiltration difficult to detect and prevent?
(Choose two)
When using Cisco AMP for Networks which feature copies a file to the Cisco AMP cloud for analysis?
On which part of the IT environment does DevSecOps focus?
An engineer configured a new network identity in Cisco Umbrella but must verify that traffic is being routed
through the Cisco Umbrella network. Which action tests the routing?
What can be integrated with Cisco Threat Intelligence Director to provide information about security threats,
which allows the SOC to proactively automate responses to those threats?
Refer to the exhibit.
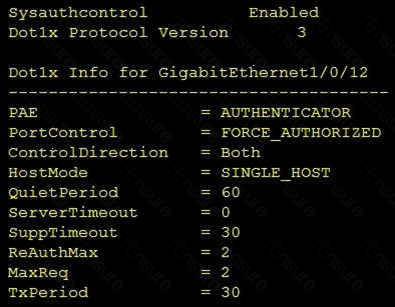
Which command was used to display this output?
The Cisco ASA must support TLS proxy for encrypted Cisco Unified Communications traffic. Where must the
ASA be added on the Cisco UC Manager platform?
Which CLI command is used to register a Cisco FirePower sensor to Firepower Management Center?
Which two probes are configured to gather attributes of connected endpoints using Cisco Identity Services
Engine? (Choose two)
Which Cisco product provides proactive endpoint protection and allows administrators to centrally manage the
deployment?
Which two key and block sizes are valid for AES? (Choose two)
In which form of attack is alternate encoding, such as hexadecimal representation, most often observed?
Which Cisco security solution protects remote users against phishing attacks when they are not connected to
the VPN?
Which feature is supported when deploying Cisco ASAv within AWS public cloud?
Which benefit is provided by ensuring that an endpoint is compliant with a posture policy configured in Cisco ISE?
Which Cisco Advanced Malware protection for Endpoints deployment architecture is designed to keep data
within a network perimeter?
What are two reasons for implementing a multifactor authentication solution such as Duo Security provide to an
organization? (Choose two)
Which Cisco AMP file disposition valid?
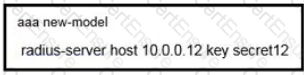
Which Cisco command enables authentication, authorization, and accounting globally so that CoA is supported on the device?
Which Cisco solution does Cisco Umbrella integrate with to determine if a URL is malicious?
Which flaw does an attacker leverage when exploiting SQL injection vulnerabilities?
Under which two circumstances is a CoA issued? (Choose two)
Which proxy mode must be used on Cisco WSA to redirect TCP traffic with WCCP?
Which SNMPv3 configuration must be used to support the strongest security possible?
Refer to the exhibit.
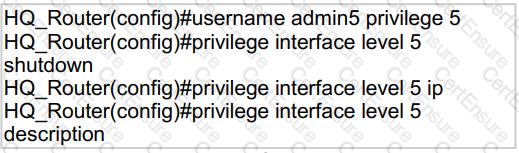
A network administrator configures command authorization for the admin5 user. What is the admin5 user able to do on HQ_Router after this configuration?
Which two capabilities does TAXII support? (Choose two)
For which two conditions can an endpoint be checked using ISE posture assessment? (Choose two)
What is the purpose of the Decrypt for Application Detection feature within the WSA Decryption options?
Refer to the exhibit.
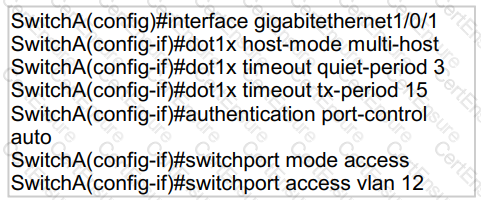
An engineer configured wired 802.1x on the network and is unable to get a laptop to authenticate. Which port configuration is missing?
What is a characteristic of traffic storm control behavior?
Elliptic curve cryptography is a stronger more efficient cryptography method meant to replace which current
encryption technology?
What is a characteristic of Cisco ASA Netflow v9 Secure Event Logging?
What are two list types within AMP for Endpoints Outbreak Control? (Choose two)
Which Cisco product is open, scalable, and built on IETF standards to allow multiple security products from
Cisco and other vendors to share data and interoperate with each other?
Which two services must remain as on-premises equipment when a hybrid email solution is deployed? (Choose two)
What is a characteristic of a bridge group in ASA Firewall transparent mode?
How is Cisco Umbrella configured to log only security events?
What is the function of Cisco Cloudlock for data security?
What is a feature of the open platform capabilities of Cisco DNA Center?
Which PKI enrollment method allows the user to separate authentication and enrollment actions and also
provides an option to specify HTTP/TFTP commands to perform file retrieval from the server?
How does Cisco Umbrella archive logs to an enterprise owned storage?
Which two deployment model configurations are supported for Cisco FTDv in AWS? (Choose two)
Which two request of REST API are valid on the Cisco ASA Platform? (Choose two)
A network administrator configures Dynamic ARP Inspection on a switch. After Dynamic ARP Inspection is applied, all users on that switch are unable to communicate with any destination. The network administrator checks the interface status of all interfaces, and there is no err-disabled interface. What is causing this problem?
Which two features of Cisco Email Security can protect your organization against email threats? (Choose two)
Which RADIUS attribute can you use to filter MAB requests in an 802.1 x deployment?
Which two mechanisms are used to control phishing attacks? (Choose two)
Refer to the exhibit.
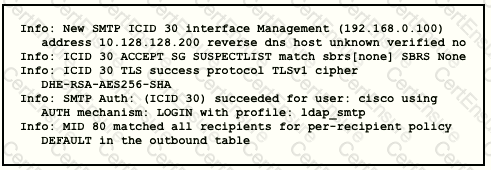
Which type of authentication is in use?
Which algorithm provides asymmetric encryption?
Which type of protection encrypts RSA keys when they are exported and imported?
What must be configured in Cisco ISE to enforce reauthentication of an endpoint session when an endpoint is
deleted from an identity group?
An engineer needs a cloud solution that will monitor traffic, create incidents based on events, and integrate with
other cloud solutions via an API. Which solution should be used to accomplish this goal?
What are two Trojan malware attacks? (Choose two)
What is provided by the Secure Hash Algorithm in a VPN?
Using Cisco Firepower’s Security Intelligence policies, upon which two criteria is Firepower block based?
(Choose two)
With which components does a southbound API within a software-defined network architecture communicate?
What is a benefit of conducting device compliance checks?
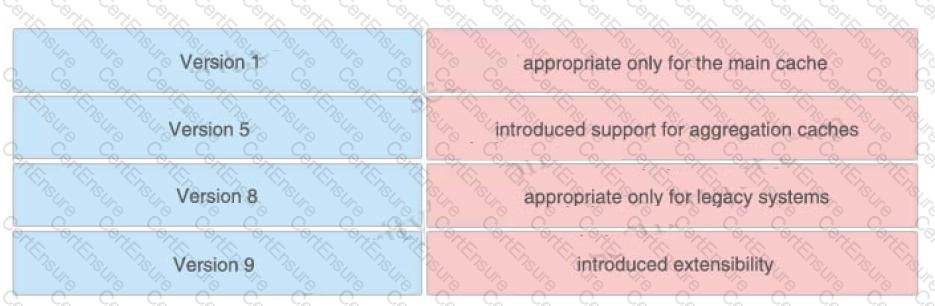
Drag and drop the NetFlow export formats from the left onto the descriptions on the right.
What features does Cisco FTDv provide over ASAv?
When planning a VPN deployment, for which reason does an engineer opt for an active/active FlexVPN
configuration as opposed to DMVPN?
Refer to the exhibit.
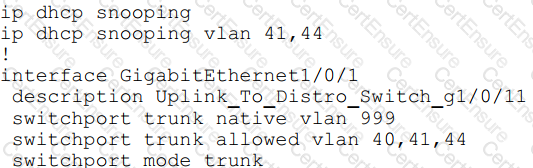
An organization is using DHCP Snooping within their network. A user on VLAN 41 on a new switch is
complaining that an IP address is not being obtained. Which command should be configured on the switch
interface in order to provide the user with network connectivity?
An engineer is configuring 802.1X authentication on Cisco switches in the network and is using CoA as a mechanism. Which port on the firewall must be opened to allow the CoA traffic to traverse the network?
What is a function of 3DES in reference to cryptography?
An organization received a large amount of SPAM messages over a short time period. In order to take action on the messages, it must be determined how harmful the messages are and this needs to happen dynamically.
What must be configured to accomplish this?
In which two ways does Easy Connect help control network access when used with Cisco TrustSec? (Choose two)
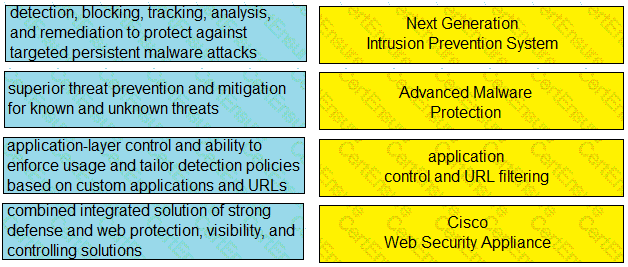
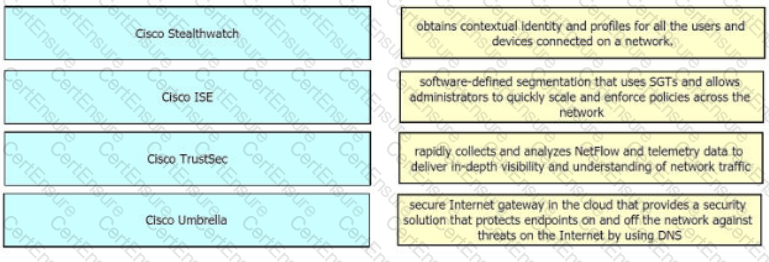
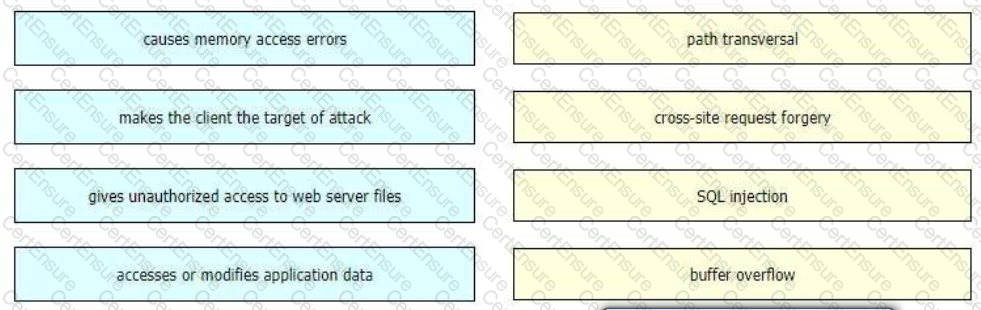
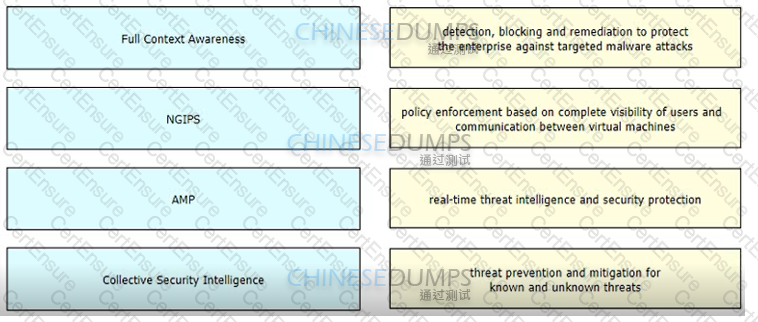
Drag and drop the capabilities from the left onto the correct technologies on the right.
An engineer is implementing NTP authentication within their network and has configured both the client and server devices with the command ntp authentication-key 1 md5 Cisc392368270. The server at 1.1.1.1 is attempting to authenticate to the client at 1.1.1.2, however it is unable to do so. Which command is required to enable the client to accept the server’s authentication key?
A user has a device in the network that is receiving too many connection requests from multiple machines.
Which type of attack is the device undergoing?
An organization recently installed a Cisco WSA and would like to take advantage of the AVC engine to allow the organization to create a policy to control application specific activity. After enabling the AVC engine, what must be done to implement this?
Which product allows Cisco FMC to push security intelligence observable to its sensors from other products?
Which cryptographic process provides origin confidentiality, integrity, and origin authentication for packets?
What is a feature of Cisco NetFlow Secure Event Logging for Cisco ASAs?
Which type of API is being used when a security application notifies a controller within a software-defined network architecture about a specific security threat?
What is the role of an endpoint in protecting a user from a phishing attack?
In which type of attack does the attacker insert their machine between two hosts that are communicating with each other?
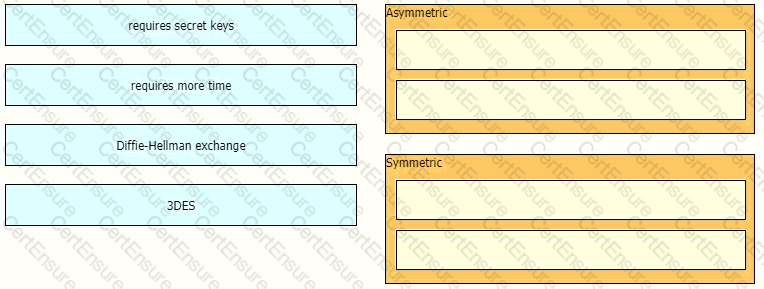
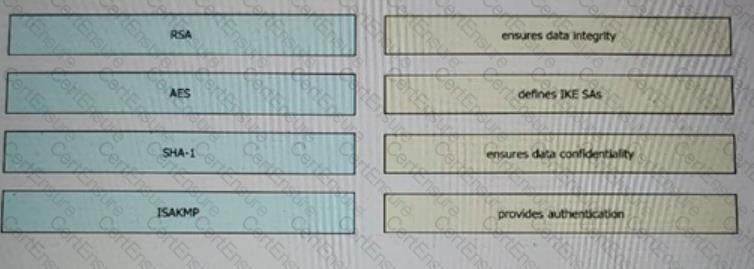 Drag and drop the VPN functions from the left onto the description on the right.
Drag and drop the VPN functions from the left onto the description on the right.
An organization is receiving SPAM emails from a known malicious domain. What must be configured in order to
prevent the session during the initial TCP communication?
An attacker needs to perform reconnaissance on a target system to help gain access to it. The system has weak passwords, no encryption on the VPN links, and software bugs on the system’s applications. Which
vulnerability allows the attacker to see the passwords being transmitted in clear text?
An administrator is trying to determine which applications are being used in the network but does not want the
network devices to send metadata to Cisco Firepower. Which feature should be used to accomplish this?
Which public cloud provider supports the Cisco Next Generation Firewall Virtual?
A switch with Dynamic ARP Inspection enabled has received a spoofed ARP response on a trusted interface.
How does the switch behave in this situation?
An engineer needs behavioral analysis to detect malicious activity on the hosts, and is configuring the
organization’s public cloud to send telemetry using the cloud provider’s mechanisms to a security device. Which
mechanism should the engineer configure to accomplish this goal?
What are two benefits of Flexible NetFlow records? (Choose two)
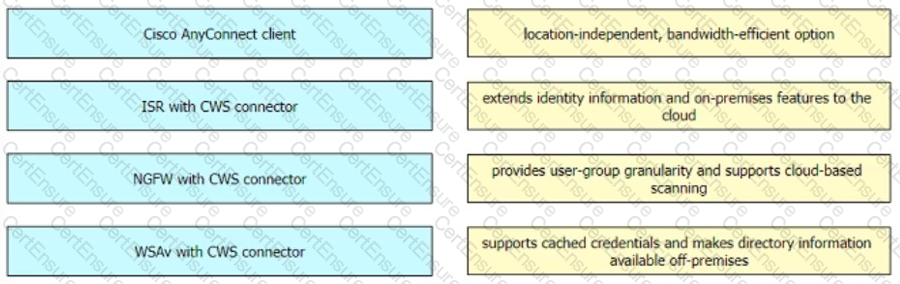
Drag and drop the solutions from the left onto the solution's benefits on the right.
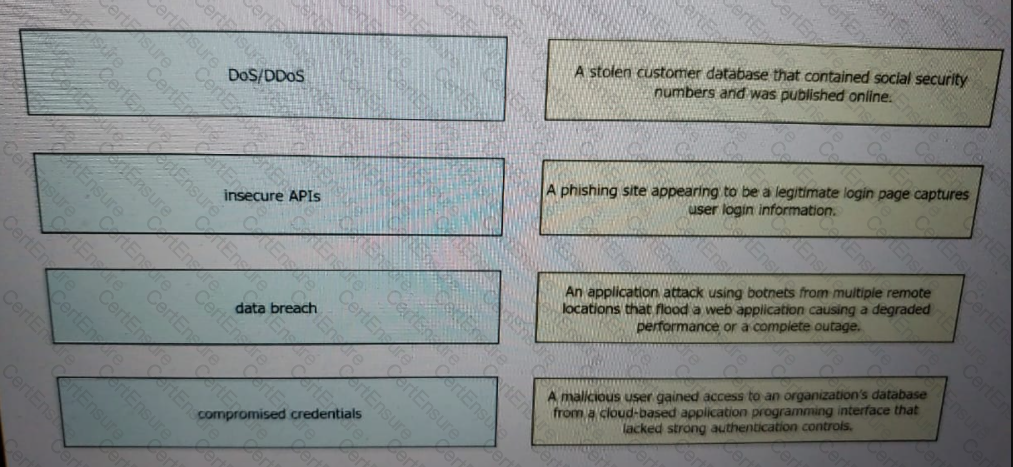
Drag and drop the threats from the left onto examples of that threat on the right
A network administrator is configuring SNMPv3 on a new router. The users have already been created;
however, an additional configuration is needed to facilitate access to the SNMP views. What must the
administrator do to accomplish this?
In which situation should an Endpoint Detection and Response solution be chosen versus an Endpoint
Protection Platform?
Which group within Cisco writes and publishes a weekly newsletter to help cybersecurity professionals remain
aware of the ongoing and most prevalent threats?
Which term describes when the Cisco Firepower downloads threat intelligence updates from Cisco Talos?
Which component of Cisco umbrella architecture increases reliability of the service?
An administrator is configuring a DHCP server to better secure their environment. They need to be able to ratelimit the traffic and ensure that legitimate requests are not dropped. How would this be accomplished?
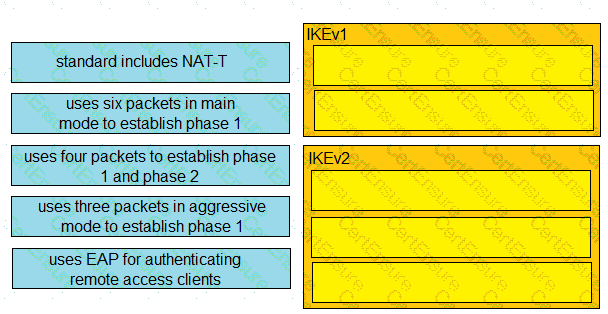
Drag and drop the descriptions from the left onto the correct protocol versions on the right.
What are two functions of secret key cryptography? (Choose two)
An organization has two systems in their DMZ that have an unencrypted link between them for communication.
The organization does not have a defined password policy and uses several default accounts on the systems.
The application used on those systems also have not gone through stringent code reviews. Which vulnerability
would help an attacker brute force their way into the systems?
A network administrator is configuring a switch to use Cisco ISE for 802.1X. An endpoint is failing
authentication and is unable to access the network. Where should the administrator begin troubleshooting to verify the authentication details?
An organization wants to secure users, data, and applications in the cloud. The solution must be API-based and
operate as a cloud-native CASB. Which solution must be used for this implementation?
Why is it important to have logical security controls on endpoints even though the users are trained to spot security threats and the network devices already help prevent them?
Which cloud model is a collaborative effort where infrastructure is shared and jointly accessed by several organizations from a specific group?
Which type of dashboard does Cisco DNA Center provide for complete control of the network?
Refer to the exhibit.
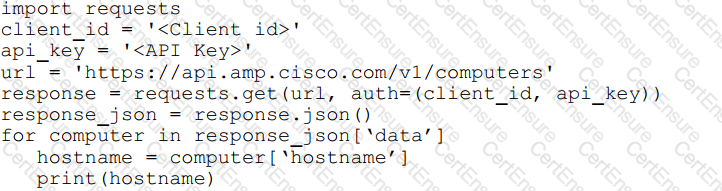
What will happen when the Python script is executed?
Drag and drop the descriptions from the left onto the encryption algorithms on the right.
Which Cisco platform ensures that machines that connect to organizational networks have the recommended
antivirus definitions and patches to help prevent an organizational malware outbreak?
What is a functional difference between a Cisco ASA and a Cisco IOS router with Zone-based policy firewall?
For Cisco IOS PKI, which two types of Servers are used as a distribution point for CRLs? (Choose two)
Which risk is created when using an Internet browser to access cloud-based service?
Which two cryptographic algorithms are used with IPsec? (Choose two)
An organization has two systems in their DMZ that have an unencrypted link between them for communication.
The organization does not have a defined password policy and uses several default accounts on the systems.
The application used on those systems also have not gone through stringent code reviews. Which vulnerability
would help an attacker brute force their way into the systems?
How does Cisco Advanced Phishing Protection protect users?
What is managed by Cisco Security Manager?
What are two DDoS attack categories? (Choose two)
What are two functions of TAXII in threat intelligence sharing? (Choose two.)
Which security solution protects users leveraging DNS-layer security?
Drag and drop the Cisco CWS redirection options from the left onto the capabilities on the right.
Which Cisco ISE feature helps to detect missing patches and helps with remediation?
An engineer needs to configure an access control policy rule to always send traffic for inspection without
using the default action. Which action should be configured for this rule?
Which threat intelligence standard contains malware hashes?
Which cloud service offering allows customers to access a web application that is being hosted, managed, and maintained by a cloud service provider?
When a next-generation endpoint security solution is selected for a company, what are two key
deliverables that help justify the implementation? (Choose two.)
When network telemetry is implemented, what is important to be enabled across all network infrastructure devices to correlate different sources?
Which service allows a user export application usage and performance statistics with Cisco Application Visibility
and control?
Which RADIUS feature provides a mechanism to change the AAA attributes of a session after it is
authenticated?
An administrator configures a new destination list in Cisco Umbrella so that the organization can block specific domains for its devices. What should be done to ensure that all subdomains of domain.com are blocked?
A company discovered an attack propagating through their network via a file. A custom file policy was created in order to track this in the future and ensure no other endpoints execute the infected file. In addition, it was discovered during testing that the scans are not detecting the file as an indicator of compromise. What must be done in order to ensure that the created is functioning as it should?
An administrator configures a Cisco WSA to receive redirected traffic over ports 80 and 443. The organization requires that a network device with specific WSA integration capabilities be configured to send the traffic to the WSA to proxy the requests and increase visibility, while making this invisible to the users. What must be done on the Cisco WSA to support these requirements?
Refer to the exhibit.
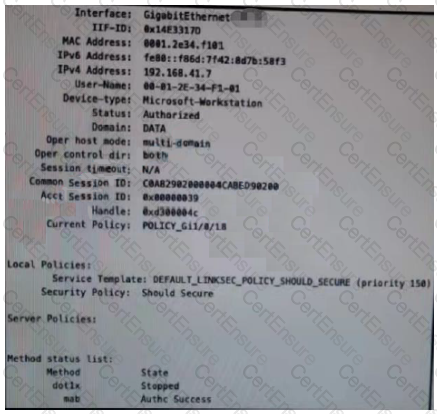
Which configuration item makes it possible to have the AAA session on the network?
An engineer needs to add protection for data in transit and have headers in the email message Which configuration is needed to accomplish this goal?
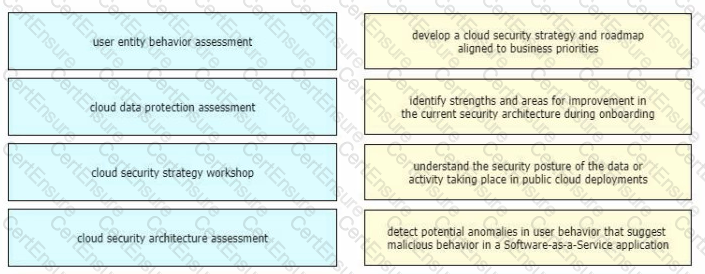
Drag and drop the cloud security assessment components from the left onto the definitions on the right.
An organization is implementing AAA for their users. They need to ensure that authorization is verified for every command that is being entered by the network administrator. Which protocol must be configured in order to provide this capability?
What is the result of the ACME-Router(config)#login block-for 100 attempts 4 within 60 command on a Cisco IOS router?
Which threat intelligence standard contains malware hashes?
An engineer is configuring Cisco Umbrella and has an identity that references two different policies. Which action ensures that the policy that the identity must use takes precedence over the second one?
In which two ways does the Cisco Advanced Phishing Protection solution protect users? (Choose two.)
What is the purpose of joining Cisco WSAs to an appliance group?
Which two parameters are used to prevent a data breach in the cloud? (Choose two.)
Which ESA implementation method segregates inbound and outbound email?
Which characteristic is unique to a Cisco WSAv as compared to a physical appliance?
Which two capabilities of Integration APIs are utilized with Cisco DNA center? (Choose two)
Which Talos reputation center allows for tracking the reputation of IP addresses for email and web traffic?
An administrator is establishing a new site-to-site VPN connection on a Cisco IOS router. The organization
needs to ensure that the ISAKMP key on the hub is used only for terminating traffic from the IP address of
172.19.20.24. Which command on the hub will allow the administrator to accomplish this?
Drag and drop the exploits from the left onto the type of security vulnerability on the right.
An engineer is adding a Cisco DUO solution to the current TACACS+ deployment using Cisco ISE. The engineer wants to authenticate users using their account when they log into network devices. Which action accomplishes this task?
Which action must be taken in the AMP for Endpoints console to detect specific MD5 signatures on endpoints and then quarantine the files?
What is the purpose of the Cisco Endpoint loC feature?
What is the most commonly used protocol for network telemetry?
Which type of DNS abuse exchanges data between two computers even when there is no direct connection?
Refer to the exhibit. What is the result of using this authentication protocol in the configuration?
What are two functions of IKEv1 but not IKEv2? (Choose two)
What is the term for when an endpoint is associated to a provisioning WLAN that is shared with guest
access, and the same guest portal is used as the BYOD portal?
An engineer must configure Cisco AMP for Endpoints so that it contains a list of files that should not be executed by users. These files must not be quarantined. Which action meets this configuration requirement?
What is a benefit of a Cisco Secure Email Gateway Virtual as compared to a physical Secure Email Gateway?
How is data sent out to the attacker during a DNS tunneling attack?
Which technology provides the benefit of Layer 3 through Layer 7 innovative deep packet inspection,
enabling the platform to identify and output various applications within the network traffic flows?
Which two components do southbound APIs use to communicate with downstream devices? (Choose two.)
Refer to the exhibit.
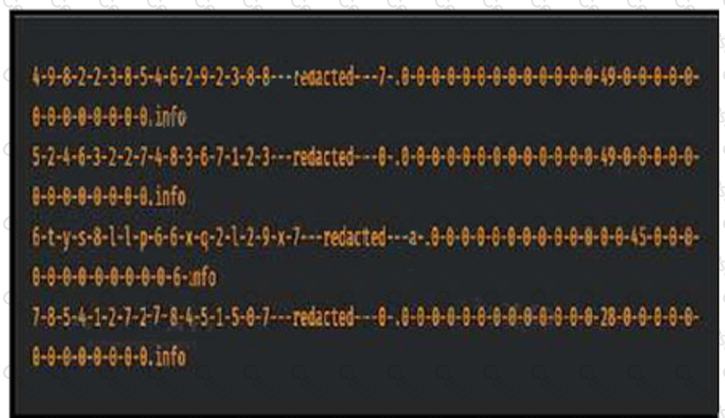
Consider that any feature of DNS requests, such as the length off the domain name
and the number of subdomains, can be used to construct models of expected behavior to which
observed values can be compared. Which type of malicious attack are these values associated with?
Which Cisco cloud security software centrally manages policies on multiple platforms such as Cisco ASA, Cisco Firepower, Cisco Meraki, and AWS?
Which capability is provided by application visibility and control?
Which role is a default guest type in Cisco ISE?
A network engineer is trying to figure out whether FlexVPN or DMVPN would fit better in their environment.
They have a requirement for more stringent security multiple security associations for the connections, more efficient VPN establishment as well consuming less bandwidth. Which solution would be best for this and why?
Which Cisco solution provides a comprehensive view of Internet domains. IP addresses, and autonomous systems to help pinpoint attackers and malicious infrastructures?
How does Cisco AMP for Endpoints provide next-generation protection?
Which solution supports high availability in routed or transparent mode as well as in northbound and
southbound deployments?
What is the default action before identifying the URL during HTTPS inspection in Cisco Secure Firewall Threat Defense software?
Which attribute has the ability to change during the RADIUS CoA?
An organization has DHCP servers set up to allocate IP addresses to clients on the LAN. What must be done to ensure the LAN switches prevent malicious DHCP traffic while also distributing IP addresses to the correct endpoints?
Refer to the exhibit.
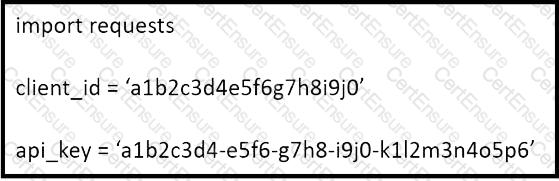
What does the API key do while working with https://api.amp.cisco.com/v1/computers?
An engineer is configuring IPsec VPN and needs an authentication protocol that is reliable and supports ACK
and sequence. Which protocol accomplishes this goal?
Drag and drop the features of Cisco ASA with Firepower from the left onto the benefits on the right.
What is a benefit of using GET VPN over FlexVPN within a VPN deployment?
An organization wants to use Cisco FTD or Cisco ASA devices. Specific URLs must be blocked from being
accessed via the firewall which requires that the administrator input the bad URL categories that the
organization wants blocked into the access policy. Which solution should be used to meet this requirement?
What is an advantage of network telemetry over SNMP pulls?
An organization wants to implement a cloud-delivered and SaaS-based solution to provide visibility and threat detection across the AWS network. The solution must be deployed without software agents and rely on AWS VPC flow logs instead. Which solution meets these requirements?
Which Cisco security solution provides patch management in the cloud?
Which technology must De used to Implement secure VPN connectivity among company branches over a private IP cloud with any-to-any scalable connectivity?